For the Support engagement, we help you produce the cybersecurity
artifacts typically needed for 510(k), De Novo, and PMA submissions. The
documents are organized so they can be uploaded directly into the latest
eSTAR template.
We align the content to FDA’s current cybersecurity expectations,
using these guidance documents as key references:
See below for summary descriptions of each deliverable:
Security Architecture Views
Visual diagrams of system components, data flows, connections, and
trust boundaries. Includes Global System View, Multi-Patient Harm View
(if applicable), Use Case Views, and Updateability View.
Cybersecurity Controls (Draft/Final)
Proposed and final security controls addressing FDA's 8 risk control
categories to mitigate identified risks.
Initial draft provided in Phase 1 for software team
implementation.
Cybersecurity Management Plan
Plan for managing cybersecurity risks throughout product lifecycle,
including development, vulnerability handling, and monitoring.
Cybersecurity Measures and Metrics
Indicators tracking security control effectiveness (e.g.,
vulnerability count, patch response time).
For new devices, outlines planned metrics only.
Threat Model
STRIDE analysis of threat actors, assets, and attack vectors, showing
potential vulnerabilities and safety impacts.
Security Risk Assessment
Risk evaluation showing traceability between vulnerabilities,
controls, and residual risks.
Cybersecurity Labeling
User documentation covering security responsibilities, diagrams,
updates, and anomaly reporting.
Software Bill of Materials (SBOM)
List of all software components and third-party libraries used in the
device.
Software Level of Support and End of Support
Support duration and end-of-life plans for each SBOM component.
Vulnerability Assessment
Review of vulnerabilities found in SBOM scan.
Assessment of Unresolved Security Anomalies
Open security issues with impact analysis and mitigation plans.
Cybersecurity Metrics Report
Addresses plan for on-going cybersecurity metrics.
Cybersecurity Testing Report
Summary of all security testing activities and results.
Penetration Testing Report
Third-party pen-test findings and recommendations with FDA-aligned
analysis.
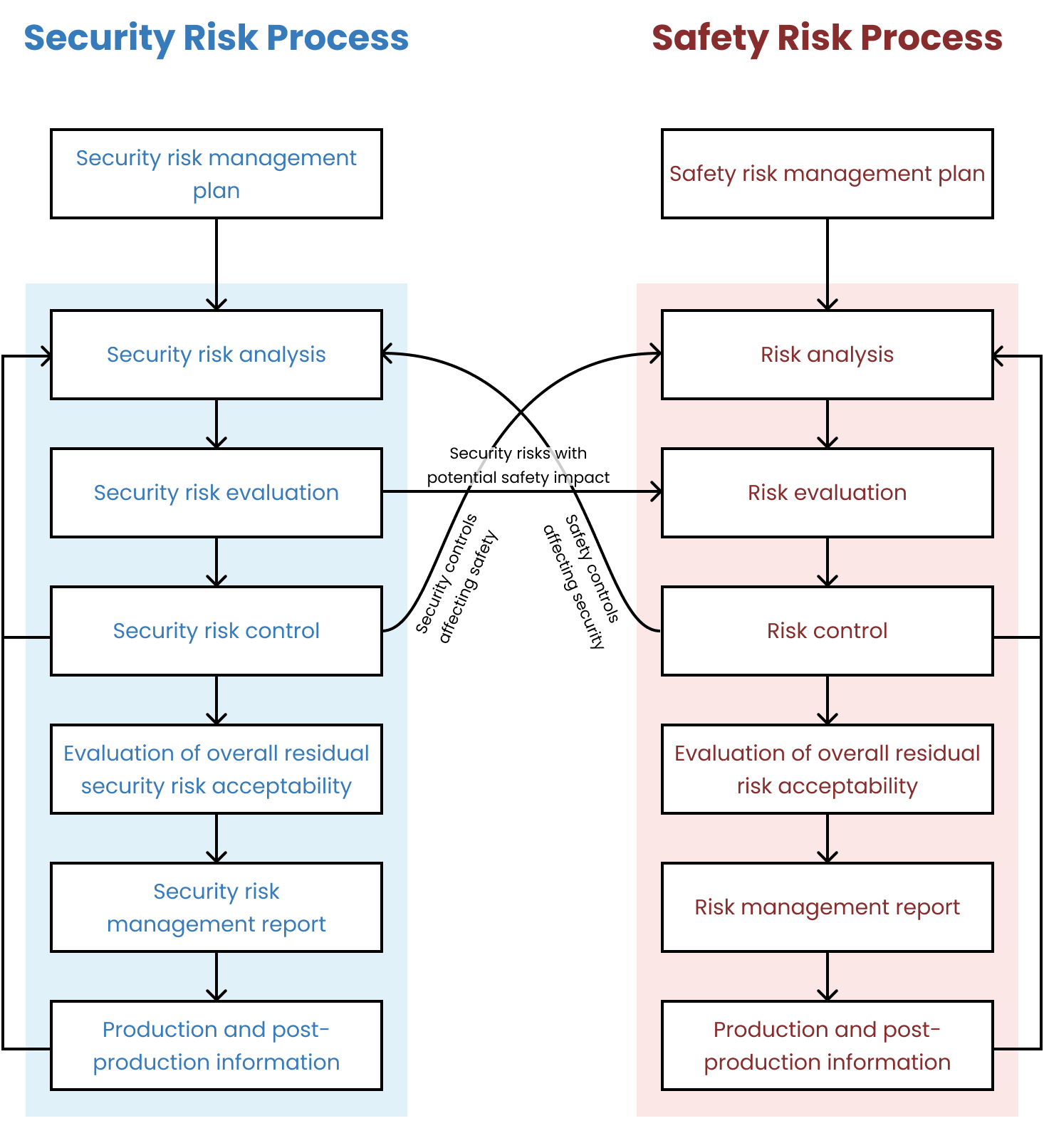
Security Risk Management Report
Final summary of all security activities providing submission-ready
overview.