Introduction 🔗
The FDA is increasingly focused on cybersecurity. Many medical-device manufacturers must now generate a Software Bill of Materials (SBOM) for each release of your device software. This document describes best practices, answers frequently asked questions, and gives examples of related to SBOMs. It is focused on the US market, although content may be relevant to other jurisdictions.
I’d like to thank Om Mahida from Medcrypt (the creators of the Helm SBOM Management and Vulnerability Monitoring tool) for reviewing this document and providing his experiences from working directly with medtech and healthcare on their SBOMs for over 5 years.
About the Author 🔗

Hi, I’m David Giese, a Partner at Innolitics. I’ve wrote this article based on my real-world experiences bringing 35+ diagnostic medical devices onto the US market. I take pride in the in-depth articles I write, and appreciate feedback and questions. I’d love to connect on LinkedIn, where I post pragmatic tips about medical-device cybersecurity for my >4k followers.
Best Practices 🔗
Here is a short list of best-practices for creating SBOMs.
- Automate the generation of your SBOM, e.g., by including its generation in your CI/CD pipeline and storing it as a build artifact.
- Include metadata about your software in the SBOM, in addition to including at least:
- The name of your company, including your company website and a contact.
- The git hash of the source code used to generate the file.
- The timestamp when the SBOM was generated.
- A short description of the component.
- Include all the fields from Framing Software Component Transparency: Establishing a Common Software Bill of Materials (SBOM) in your SBOM.
- Use a tool to continuously monitor for vulnerabilities in the SBOM for all devices in the field.
- Include both a human-readable and machine-readable version of your SBOMs in your regulatory submissions.
- Have a process for periodically reviewing the identified vulnerabilities and systematically evaluating their risk to patient safety.
Basics 🔗
What is an SBOM? 🔗
An SBOM, or Software Bill of Materials, is a comprehensive list of components, libraries, and dependencies used in a software system.
What is the purpose of an SBOM? 🔗
SBOMs provide transparency about the software's composition, making it easier to track and manage potential security vulnerabilities, licensing requirements, and other risks associated with software usage. An SBOM can include information about open-source and commercial components, as well as their respective versions and licensing information.
Do we need to include an SBOM in our pre-market submission? 🔗
If you’re marketing your device in the United States and your device contains software, then most likely you need to include an SBOM in your 510(k), De Novo, or PMA submission.
The FDA guidance recommends that you include an SBOM for all devices.
If your medical-device meets the regulatory definition of a “cyber device”, then you must include an SBOM. In general, a “cyber device” is one that has the ability to connect to the internet and has “any such technological characteristics … that could be vulnerable to cybersecurity threats”. If your device contains software and has any external ports (even USB ports), the FDA will almost certainly consider it a “cyber device.”
Do we need to distribute SBOMs to our customers? 🔗
The FDA regulations do not explicitly require that you distribute an SBOM, although your customers will likely request it. The FDA guidance does suggest that it be made available:
Manufacturers should provide or make available SBOM information to users on a continuous basis. If an online portal is used, manufacturers should ensure that users have up-to-date links that contain accurate information. The SBOM should be in a machine-readable format.
Does the FDA specify a particular SBOM format? 🔗
No. FDA does not specify a particular SBOM format. They do, however, require that whatever format you use include the “Baseline Attributes” from Framing Software Component Transparency: Establishing a Common Software Bill of Materials (SBOM), which was published in October 2021.
They also require a couple of additional fields. See the later questions for more details.
How often do we need to update our SBOM? 🔗
FDA expects that the SBOM be updated as the software is updated. Thus, you must create a new SBOM for each release of the software, especially if the versions of the software components have changed since the last release.
Should we create an SBOM early in our development process? 🔗
In our experience, many medical-device manufacturers don’t produce an SBOM until it is needed for their first FDA submission. This is a missed opportunity. Since we suggest automating your SBOM-generation, you may as well set this up early in the process. Once you have your SBOM, you can begin scanning it for vulnerabilities during development. This ensures that if there are any unsupported, outdated dependencies with unfixed vulnerabilities, you’ll catch them early in the development process.
Here’s a scenario I’ve run into several times:
- A junior engineer adds “Poorly Supported Package v0.3.5” to a project.
- This package depends on other widely used and out-dated libraries.
- A company waits until their 510(k), and generates an SBOM.
- They start writing their Security Assessment of Unresolved Anomalies and they realize there is a bad vulnerability they can’t ship.
- You now need to do one of the following:
- Fork and update “Poorly Supported Package v0.3.5”
- Rip out “Poorly Supported Package v0.3.5”
- Bend yourself in circles trying to mitigate the vulnerability
All of this could have been avoided if you set up SBOM generation and vulnerability monitoring earlier in the development process and integrated it into your development process. This is why the FDA has gotten increasingly focused on using a “Secure Product Development Framework” in their guidance.
Do you need OTS Software Documentation for every item on your SBOM? 🔗
No, not typically. See our Off-The-Shelf Software: Best Practices, FAQs, and Examples document for much more details on this topic.
What is a CBOM? 🔗
CBOM stands for Cybersecurity Bill of Materials. The FDA introduced this term in their 2018 draft guidance, but in they switched to the more standard SBOM term in their 2023 final guidance. You may see this term used in older articles.
Do you have any other resources for learning about SBOMs? 🔗
Yes! Here are a few more good reads:
- How-To Guide for SBOM Generation
- 2023 IMDR Guidance “Principles and Practices for Software Bill of Materials for Medical Device Cybersecurity”
- Framing Software Component Transparency: Establishing a Common Software Bill of Materials (SBOM)
- 2021 Software Identification Challenges and Guidance
- 2021 Survey of Existing SBOM Formats and Standards
- 2024 Data Normalization Challenges and Mitigations in SBOM Processing
Generating an SBOM 🔗
How do we create an SBOM? 🔗
The basic process involves these steps:
- Select an SBOM file-format.
- Identify the third-party components, libraries, and dependencies used in your software.
- Gather the information needed to fill in the required attributes for your SBOM format (ideally automatically, using a tool).
- Insert the information into your SBOM file (ideally automatically).
- Validate your SBOM file.
We suggest automating the process and incorporating it into your CI/CD pipeline.
Usually some components are not tracked anywhere else and need to be manually added.
What SBOM file format should we use? 🔗
There are two widely-used SBOM formats:
- CycloneDX
- SPDX
We recommend the CycloneDX format. It has good tooling support and it’s specification is short and more developer friendly. (Compare it to the SPDX specification.) The CycloneDX format is focused on security use-cases while the SPDX historically focused on open-source license tracking.
That said, some tools (e.g., GitHub) produce SPDX files, and it is also industry standard. Future updates to the SPDX standard are likely to bring it closer to the CycloneDx standard.
If you’d like a more in-depth comparison of the formats, the 2021 Survey of Existing SBOM Formats and Standards is a good read.
(Note that most people aren’t really using the SWID format anymore.)
What Information do we need to include for each component in our SBOM? 🔗
FDA requires your SBOM to address the “Baseline Attributes” from Framing Software Component Transparency: Establishing a Common Software Bill of Materials (SBOM), which was published in October 2021. They also require a couple of additional fields. We’ve collected all of this information into the following table for your convenience:
| Name | Description |
|---|---|
| Author Name | The author of the SBOM. The author may not always be the supplier, which indicates that the SBOM was not created by the supplier. |
| Timestamp | Date and time when the SBOM was last updated. Timestamp should be updated when an SBOM entry is changed, which includes initial creation. Timestamp should be consistent across time zones and locales and use a common international format, such as ISO 8601. |
| Supplier Name | Name or other identifier of the supplier of a component in an SBOM entry. Supplier Name should include some capability to handle multiple names or aliases. When the author and supplier are the same, the supplier created an SBOM for their own component. When the author and supplier are different, the author is making claims or assertions about a component for which the author is not the supplier. Supplier identification is not further specified in this document, but may be a significant contributor to achieving component identification at scale. |
| Component Name | Name or other identifier of a component. Component Name should include some capability to handle multiple names or aliases. Suppliers (or authors) define components and their names. Component names can convey supplier names. Component (and Supplier) Names can also be conveyed using a generic namespace:name construct. One consideration is to use the Supplier Name as the namespace designator. |
| Version String | Version of a component. Version information helps to further identify a component. Suppliers and Authors are free to choose a versioning scheme; one suggestion is Semantic Versioning. If a component does not initially have a version string, authors should create one. |
| Component Hash | Cryptographic hash of a component. A cryptographic hash is an intrinsic identifier for a software component. Digital signatures can be used in place of hashes and provide stronger integrity and authenticity, but add complexities including key management and signature verification. In addition to hash values, it must be clear to SBOM consumers as to how the hash was generated so that it can be reproduced. For example, the Software Package Data Exchange (SPDX) format specifies a Package Verification Code that creates a hash of hashes for individual file components. SBOM formats are responsible for specifying how to produce hashes. It is possible, and may be beneficial, to provide multiple hashes for a component or collections of components. Suppliers and authors choose how to define components, which in turn defines the scope of the hash. For example, an SBOM could include a hash for a source component, a hash for the compiled binary form of that component, and a hash for a collection of components. As noted previously, Component Hash is a recommended, but not required, Data Field element in The Minimum Elements For a Software Bill of Materials (SBOM). We don’t usually include this field in our human-readable SBOM tables. |
| Unique Identifier | Additional information to help uniquely define a component. A unique identifier can be generated relative to some globally unique hierarchy or namespace or reference an existing global coordinate system. Some systems that could be used as unique identifiers include Common Platform Enumeration (CPE), Package URL (PURL), Universal Unique Identifier (UUID) (also known as Globally Unique Identifier [GUID]), and Software Heritage ID (SWHID). Component Hash may effectively function as a Unique Identifier. |
| Relationship | The relationship between components is inherent in the design of the SBOM model. The default relationship type is includes. This represents the inclusion of or dependency on a separate upstream component. To simplify presentation, this document reverses the direction of the relationship to included in. The choice of direction is not important to the model, as long as one direction is chosen and used consistently. A relationship type of primary is used when a component has no upstream dependencies identified in the SBOM. The primary component defines the subject of the SBOM, including cases where the SBOM only includes one component. Other types of relationships are discussed briefly in Section 2.5 of the NTIA document. |
| Level of Support* | The software level of support provided through monitoring and maintenance from the software component manufacturer (e.g., the software is actively maintained, no longer maintained, abandoned); and |
| End of Support Date* | The software component’s end-of-support date. |
*These last two items are not mentioned in the NTIA SBOM document, but are requested by FDA. They may be included in a separate document, which we call the SBOM Support Report. See the section below on this topic.
Can we upload a machine-readable SBOM in our regulatory submissions? 🔗
Yes, the FDA’s new eSTAR format allows for machine-readable attachments. However, as of 2023, the FDA has been asking for human-readable (e.g., a PDF or Excel file) versions of the SBOM as well. JSON doesn’t cut it.
If you only have a human-readable SBOM, then a machine-readable format is not required (a Lead Cybersecurity Specialist at FDA said this in a talk I attended in February 2024).
How do you create a human-readable SBOM? 🔗
We have some open-source python scripts that we maintain to help us do this.
What components should be included in our SBOM? 🔗
This is a difficult question, as there are several layers of components that could in theory be included. Here is a list of types of components that could be included in an SBOM, starting with the most basic to the most comprehensive:
- Language-level dependencies (e.g., Tensorflow v2.9.1)
- Dependencies of your language dependencies (e.g., if package A depends on package B, be sure to include package B too.)
- System dependencies (e.g., Python v3.10.3)
- The operating system
- External cloud services
- Compilers
Hypothetically, one should include all of these dependencies in a very robust SBOM. However, keeping up with all of these dependencies takes a lot of effort. Furthermore, as you go down the list the value of including the components decreases. Thus, given limited resources we suggest focusing on dependencies that are higher risk. This typically means at least levels (1) and (2), and ideally levels (3) and (4) also. We don’t typically include levels (5) and (6).
FDA does say in their guidance that “upstream software dependencies that are required/depended upon by proprietary, purchased/licensed, and open-source software” must be included. I interpret this to mean (1), (2), (3), and (4).
Why not include external cloud services (e.g., AWS S3) in the SBOM? 🔗
You certainly can include them. However, the purpose of the SBOM is to enable you to track and upgrade dependencies. Therefore, if there is no way to upgrade the dependency, then it’s not nearly as useful to track vulnerabilities in the tool using your SBOM.
For example, imagine if you were to add AWS S3 to your SBOM. You then receive a vulnerability alert for it. It is reasonable to think that AWS will be fixing the issue and upgrading their service as quickly as they can anyway. In the mean time, there’s nothing you could do.
The main counter argument to this is that at least you would know there is a vulnerability and you could turn off your service or switch to another provider temporarily. Practically, I don’t think this would be useful in most cases.
Is it okay to have multiple SBOMs? 🔗
FDA appears to expect a single SBOM. Note that you can merge SBOMs together using tools such as cyclonedx-cli. Consider using a hierarchical merge when appropriate.
Should we automate the generation of our SBOM? 🔗
Yes, we suggest that you automate the generation of your SBOM, especially if your software has more than a handful of dependencies. For example, most software that’s built using a container solution such as Docker will have hundreds or thousands of components. Updating this by hand isn’t really feasible.
Furthermore, FDA requires most manufacturers to provide periodic security updates to their software. Automating your SBOM generation will help you keep your SBOM up to date as you release. Your engineers will likely not want to generate an SBOM by hand.
We suggest generating your SBOM as a build artifact in your continuous integration pipeline.
One downside to automatically generating an SBOM is that you may give up some control over what components are included. For example, if you combine all of your development dependencies and production dependencies into a single requirements.txt file for a Python project, then your SBOM may include your development dependencies. As a result, when you or your customers scan the SBOM for vulnerabilities, you’ll have false positives that you need to address.
If you generate an SBOM automatically, you at least want to have some mechanism for black listing the inclusion of irrelevant components so that you can (over time) reduce false positive vulnerabilities.
How do you automate the generation of an SBOM? 🔗
There is a growing suite of tools you can use to automate your SBOM generation process.
FOSSA is a great paid version with a free-tier that is often sufficient for the first submission. They also have a nice vulnerability monitoring tool.
GitHub supports generating SBOMs automatically.
Amazon Inspect can produce SBOMs from EC2 and Lambda instances.
Tools like Syft or docker scout can generate SBOMs from container images or filesystems. (Here’s an article about generating SBOM’s as part of your Docker build.)
We haven’t used them ourselves, but one of our clients had good things to say about Ketryx.
There are also “lower-level” tools that operate on a language-level. For example, if you have Python language dependencies, you can import them from your requirements.txt file.
How do you automatically generate an SBOM for a docker container? 🔗
Here’s some example bash commands showing how to create an SBOM for two docker images and to then combine them into a human-readable SBOM for an FDA submission.
Note you’ll need docker installed as well as our open-source python script.
docker load -i my-docker-image1_v1.0.0.tar
docker load -i my-docker-image2_v1.0.0.tar
mkdir child-sboms
docker sbom my-docker-image1:v1.0.0 --format spdx-json > child-sboms/sbom1.json
docker sbom my-docker-image2:v1.0.0 --format spdx-json > child-sboms/sbom2.json
python gen_sbom.py child-sboms sbom.xlsx
SBOM Support Report 🔗
What is the SBOM Support Report? 🔗
The FDA asks for a few additional pieces of information that are typically included in a separate document alongside your SBOM, which we refer to as the "SBOM Support Report". This includes the level of support and end-of-support date for each software component, as mentioned in the table above.
Although this information can be included in the SBOM itself, we often find it’s simpler to just provide it as a separate document.
How do you handle level-of-support or the end-of-support-date for open source packages? 🔗
The easy approach is to say “N/A open-source software”. FDA has often not questioned this approach.
While it is true that many open-source packages don’t have explicit levels of support and end of support dates, some do. If you want to be more conservative, you would have to look up this information for each open-source library. If you go through the open-source packages one-by-one, you can look up the relevant EOS and level of support details.
A pragmatic middle ground is to only look up this information for the essential packages you use that would be difficult to upgrade or replace quickly if there were a major cybersecurity vulnerability. After all, this is why FDA wants you to look up this information: they want to be sure you can patch cybersecurity vulnerabilities quickly.
See the examples at the bottom for a more robust approach to gathering this information.
Is there a way to automate looking up the level-of-support or the end-of-support-date? 🔗
We’ve never been able to find a way to do this reliably. The flexera product has a database you could use.
The xeol open-source product is also interesting, but imature.
We’ve also had some luck using ChatGPT to get us started on the process.
Distributing SBOMs 🔗
Does the FDA suggest how SBOMs are distributed? 🔗
The only details the FDA provides regarding the distribution of SBOMs are found in the 2023 Cybersecurity Guidance:
Manufacturers should provide or make available SBOM information to users on a continuous basis. If an online portal is used, manufacturers should ensure that users have up-to-date links that contain accurate information. The SBOM should be in a machine-readable format.
How are SBOMs usually distributed? 🔗
This is an unsolved problem and there are several alternative ways to distribute SBOMs. We suspect in a few years a standard approach will be settled upon.
Here is a nice table of alternative approaches, taken from the IMDRF Draft SBOM Guidance:
| Method of Distribution | Advantages | Disadvantages |
|---|---|---|
| Included in the Customer Security Documentation from the manufacturer | • No specialized tools required | • Not automated • Documentation must be updated frequently and distributed to the user • There needs to be a way to link the document back to the device itself (strong asset management) • Less control over SBOM access |
| Provided by the manufacturer as a separate (electronic) document | • No specialized tools required • More control over SBOM access • Preferably machine readable |
• Not automated • Documentation must be updated frequently and distributed to the user • There needs to be a way to link the document back to the device itself (strong asset management) |
| Accessible from the medical device through a display, reference (indirectly) or download | • Always the correct version • Under control of the user • More control over SBOM access |
• Not automated • Requires access to the device to be able to access the information • The device might not have a means to extract the information (e.g. user interface, USB port, network connectivity) • Requires sufficient space on the device |
| Accessible from an API on the medical device | • More control over SBOM access • Can be used in an |
• API standards remain undefined • Requires tooling • Requires connectivity |
| Manufacturer-managed Repository | • More control over SBOM access • Can be used in an automated process |
• Customers have to check multiple manufacturer sites/repositories for information |
| Centralized Repository | • More streamlined way for customers to access information (i.e., don’t have to check as many individual manufacturer sites/repositories) • Can be used in an automated process |
• Intellectual property, liability, and other considerations for the manufacturer when using a 3rd party service • Challenges with versioning as some organizations may have multiple versions of the same device with different update status and so will need to have access to all applicable SBOMs, not just the newest version |
How do you recommend we distribute our SBOM? 🔗
For early stage startups with limited resources, we recommend starting with a very simple approach: Maintain all of your SBOMs for each version of your software in a “Manufacturer-managed Repository”. (E.g., these can be release artifacts stored in GitHub with your built system images.) Then, include an email address in your user manual where manufacturers can request the SBOM for a particular version of the software. We’d then react to customer or FDA feedback before adopting a more complex distribution method.
For example, FDA pushed back on this approach (August 2024) for one of our submissions, stating:
An SBOM in a machine-readable format for users to effectively manage their assets, to understand the potential impact of identified vulnerabilities to the medical device system, and to deploy countermeasures to maintain the device’s safety and effectiveness. While we acknowledge you have stated a user is able to request the SBOM via email, this documentation should be readily available to the end user at all times. Please provide the SBOM to the end user as part of the device system labeling.
If you’re more risk averse, then you can adopt a more complex distribution approach out of the box.
For example, tools such as FOSSA provides an SBOM Portal.
Vulnerability Monitoring 🔗
Do we need to do monitor our SBOM for vulnerabilities? 🔗
Yes, you must
design, develop, and maintain processes and procedures to provide a reasonable assurance that the device and related systems are cybersecure, and make available postmarket updates and patches to the device and related systems to address—(A) on a reasonably justified regular cycle, known unacceptable vulnerabilities; and (B) as soon as possible out of cycle, critical vulnerabilities that could cause uncontrolled risks.
Thus, you need some mechanism to scan your SBOM for known vulnerabilities.
What are good tools for finding vulnerabilities using an SBOM? 🔗
GitHub’s Dependabot may be used in certain cases, although as of April 2023 it only supports certain package ecosystems.
Open-source tools include Dependency Track and Trivy.
Fossa, Black Duck, and Snyk are good paid options to consider.
Will the FDA scan our SBOM? 🔗
We haven’t seen any evidence of the FDA doing this, but it wouldn’t surprise us if they start doing this. The FDA does expect that you have evaluated the safety risk associated with any known vulnerabilities. One approach is to list the known vulnerabilities alongside your Unresolved Software Anomalies.
Will our customers scan our SBOM? 🔗
It is increasingly likely that sophisticated HDOs will rely on SBOMs as well as independent vulnerability scanners to identify vulnerabilities in their medical devices.
Thus, you need to be careful to not include packages (e.g., development dependencies) in your SBOM which will cause unnecessary false alarms.
Is it acceptable to monitor vulnerabilities independently from our SBOM? 🔗
Yes, we believe it is acceptable to monitor cybersecurity vulnerabilities in your dependencies using a mechanism apart from the SBOM. For example, if your SBOM is generated from your requirements.txt, and a vulnerability monitoring tool monitors the requirements file directly, that should be fine. FDA seems to recognize this [emphasis added]:
Because vulnerability management is a critical part of a device’s security risk management processes, an SBOM or an equivalent capability should be maintained as part of the device’s configuration management, be regularly updated to reflect any changes to the software in marketed devices
Examples 🔗
The following examples show how to handle some common situations with SBOM generation when using CycloneDX. Note that the examples are not valid standalone SBOMs since they do not include some mandatory metadata, such as the bomFormat, speVersion, or version.
Your Device 🔗
It’s helpful to include the name and version of your medical device software in the SBOM metadata so that it’s easy to identify which version of your software the SBOM applies to. This information goes inside the metadata.component field. See here for details. Here’s an example that includes other metadata suggested by the NTIA:
{
"metadata": {
"timestamp": "2060-06-09T00:33:20+0000",
"authors": {
"name": "Medical Device Manufacturer Name",
"url": "https://yourwebsite.com"
},
"supplier": {
"name": "Medical Device Manufacturer Name"
"url": "https://yourwebsite.com"
},
"component": {
"type": "application",
"name": "Medical Device Name",
"author": "Medical Device Manufacturer Name",
"version": "1.0.5"
}
},
}
The 2013 Visual C++ Redistributable Package 🔗
The Visual C++ Redistributable Package is not included in any of the purl types, so we searched the CPE database for it. We found match for the Visual Studio 2017 runtime, but the 2013 runtime was not present. Thus, we copied the CPE identifier for the 2017 runtime and updated the year number as a best guess attempt at identifying this dependency. The “name” field is a best guess based on the CPE string. The “type” is set to “library” despite the fact that the CPE identifier begins with “a” (for application). This is because the runtime isn’t really an application.
{
"components": [
{
"type": "library",
"name": "visual_studio",
"cpe": "cpe:2.3:a:microsoft:visual_studio:2013:-:*:*:*:*:*:*"
}
]
}
Python 🔗
None of the purl package types apply to Python itself, thus the CPE identifier was used. A few searches of the CPE database turned up a match. This can be included as a CycloneDX component as follows:
{
"components": [
{
"type": "application",
"name": "python",
"cpe": "cpe:/a:python:python:3.6"
}
]
}
Documentation Supporting Software Bill of Materials 🔗
The following content would go in a separate document, in addition to the SBOM, to provide the EOL and Level of Support items as required by FDA’s guidance.
Below we outline EOL and support levels for the major software components used to implement the system items described in DOC-0023 System and Software Architecture Diagram. Note that most open source software does not advertise an end-of-life date for each version or for most versions. Instead, major deprecations are only typically published when a piece of open-source piece of software is widely used and undergoing a major version change.
| Dependency | EOL | Level of Support |
|---|---|---|
| Docker | NA - Docker does not publish a preset deprecation schedule. However, they do aim for at least a 6-month advance warning for any versions that are moving to be deprecated. | We are using the community version of Docker, which does not come with guaranteed support options. However, Docker does offer a commercial subscription to receive guaranteed support responses. They provide a high level of general software quality, in terms of testing, documentation, and following a streamlined release process to address vulnerabilities and bugs. |
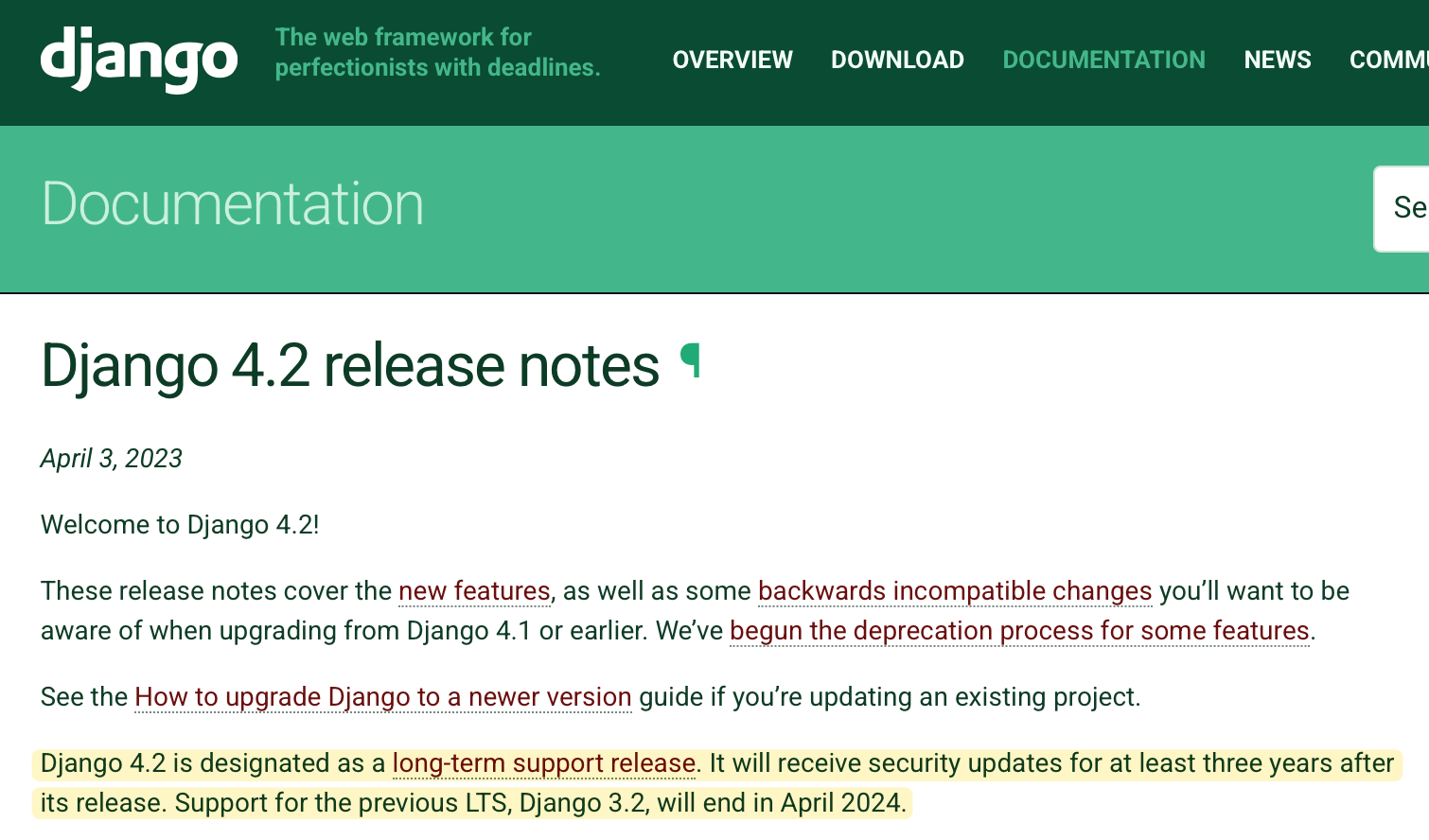
| Django | Major version (v5) will be EOL April 2025 | Commercial support is not available. However, it is a large, well-maintained open-source project, with a high level of general software quality, in terms of testing, documentation, and following a streamlined release process to address vulnerabilities and bugs. |
| React | React does not provide a preset deprecation schedule. However, based on past releases, the major version of React used by the device (v18), will have active support for an additional year. |
Commercial support is not available. However, it is a large, well-maintained open-source project, with a high level of general software quality, in terms of testing, documentation, and following a streamlined release process to address vulnerabilities and bugs. |
| Nginx | The currently installed version of nginx, 1.27, will reach EOL in May 2025, based on the current release schedule. The device will receive a patch release prior to EOL, in order to upgrade and continue receiving security patches. |
Commercial support is available for NGINX, through f5, but we are not using it. However, it is a large, well-maintained open-source project, with a high level of general software quality, in terms of testing, documentation, and following a streamlined release process to address vulnerabilities and bugs. |
| FreeSurfer | FreeSurfer does follow a regular deprecation schedule, nor do they publish EOL dates in advance. | No commercial support is offered. However, FreeSurfer is a research-backed, well-maintained piece of software, with an active network of community supporters. |
| PostgreSQL | PostgreSQL has a published release schedule. Based on this schedule, our device’s major version of PostgreSQL (v16), will be supported until November 2028. | PostgreSQL does offer commercial support, through third parties, but we are using the community version, so we don’t have a dedicated support team from the vendor. However, they provide a high level of general software quality, in terms of testing, documentation, and following a streamlined release process to address vulnerabilities and bugs. |
| Celery | Celery does not publish an EOL schedule, nor do they follow a regular pattern for deprecating past releases. | Commercial support is not available. However, it is a large, well-maintained open-source project, with a high level of general software quality, in terms of testing, documentation, and following a streamlined release process to address vulnerabilities and bugs. |
| NextJS | NextJS does not publish an EOL schedule. However, based on past release cycles, our device’s major version of NextJS (v14) will be supported for another year. | Commercial support is not available. However, it is a large, well-maintained open-source project, with a high level of general software quality, in terms of testing, documentation, and following a streamlined release process to address vulnerabilities and bugs. |
For any item in the DOC-0025 Software Bill of Materials but not in the above table, the following applies:
- The EOL is indeterminate (e.g. most open-source software does not adhere to a known EOL schedule)
- The level-of-support is not guaranteed and/or undocumented (e.g. most open-source software does not offer paid support and support might only come from the open-source community, not official team members)
Revision History 🔗
| Date | Summary of Change |
|---|---|
| 2 June 2022 | Initial Version |
| 7 June 2023 | Updated on June 7, 2023 to reflect the newest FDA regulations and guidance, and particularly section 524B(b)(3) of the FD&C Act. |
| 12 October 2023 | Updated to reflect the 2023 Final Cybersecurity Guidance and add suggestions as our recommendations have evolved. Added a section about SBOM distribution. |
| 4 March 2024 | Refined answers to a few questions. Included a copy of the minimal SBOM components from the NTIA SBOM document. Added a question about generating SBOMs in development. Added a note about CBOMs. |
| 8 August 2024 | Added example of generating SBOMs for two docker containers. Incorporated some FDA feedback from recent submissions. Deleted some older very detailed questions about component identification. |
| 30 October 2024 | Add questions about tracking cloud services in your SBOM. |
| 17 December 2024 | Add some questions and examples for the software EOS and Level of Support information. |
| 28 January 2024 | Add more detailed answers for handling EOS and Level of Support Date information. |