Medical-device cybersecurity regulations, threat modeling, SBOMs, vulnerability monitoring, and more
FeaturedArticleAI/ML
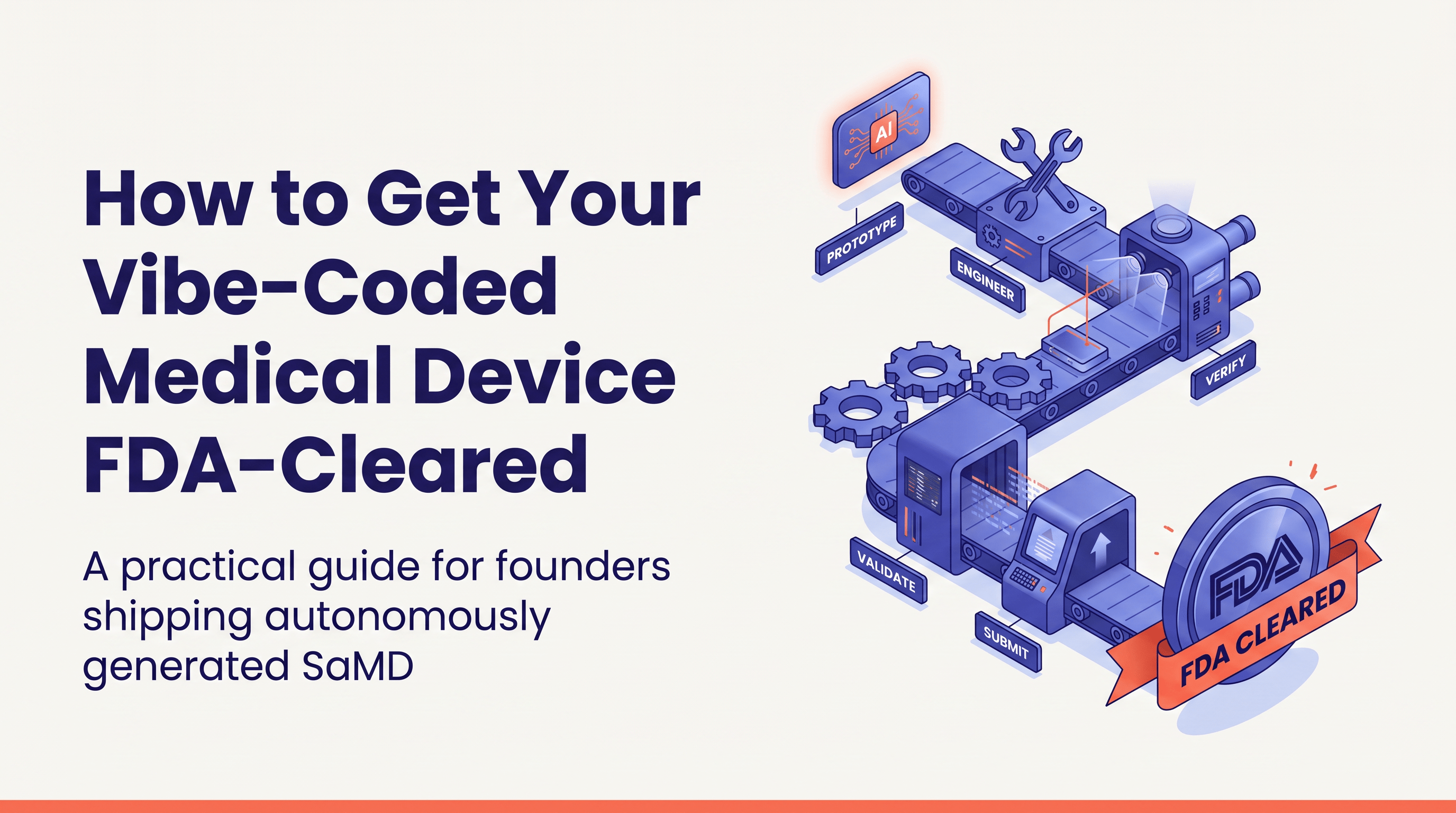
AI-assisted medical device development is FDA-compliant when done right. The obstacle isn’t regulation. It’s the messy codebase...
 Yujan Shrestha
Yujan Shrestha
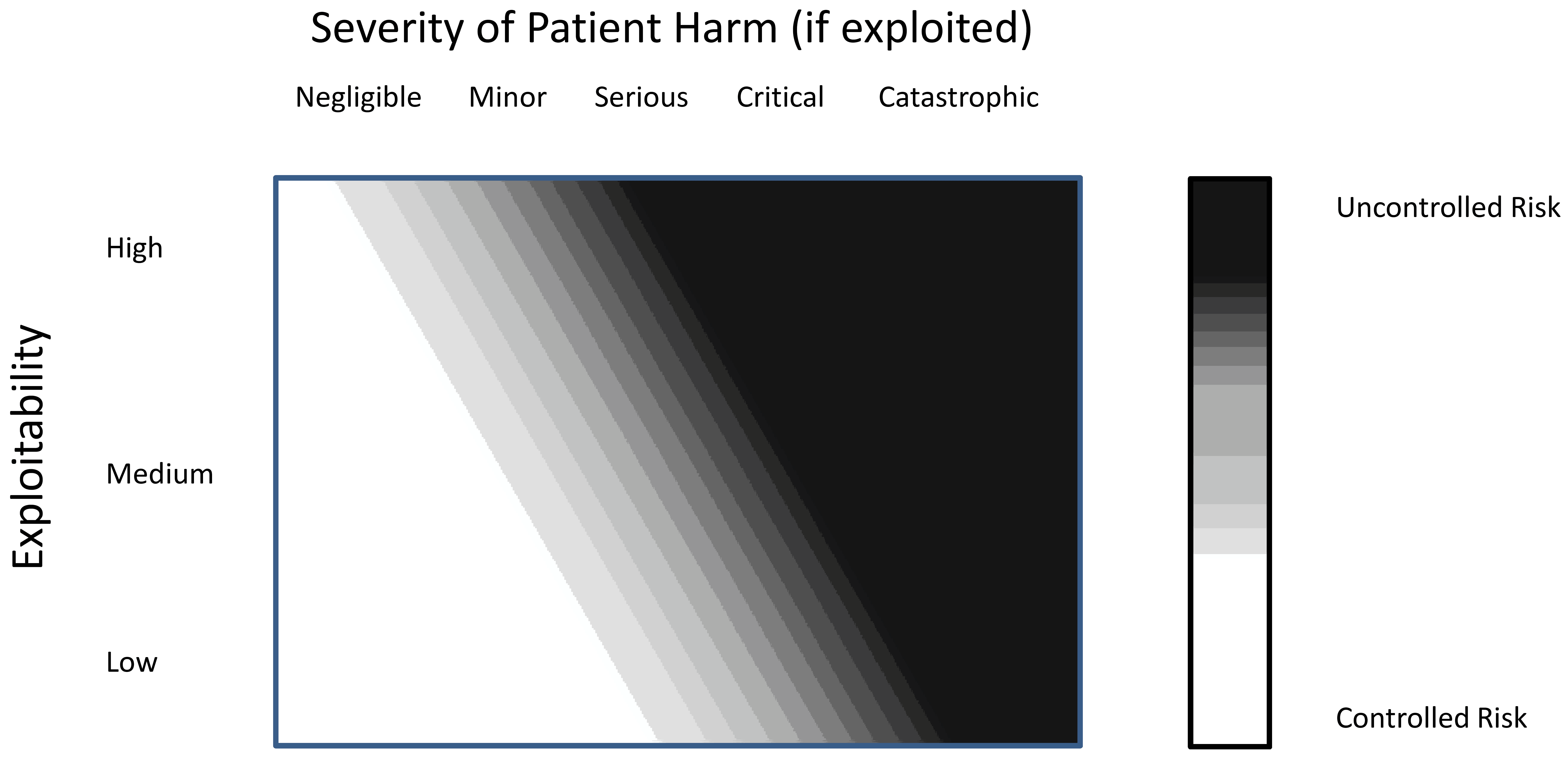
FeaturedArticleCybersecurity
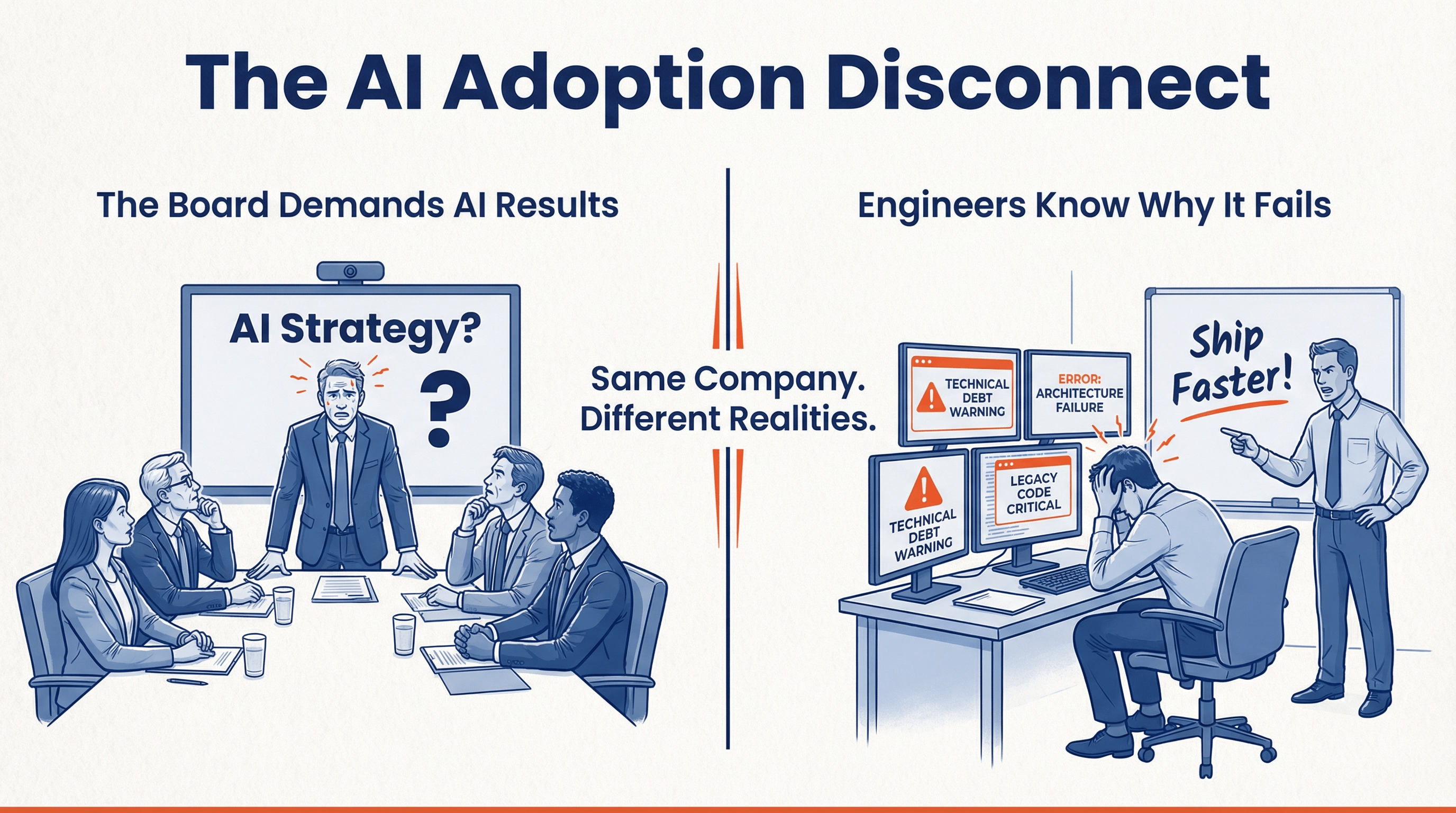
This article provides an in-depth exploration of medical device cybersecurity requirements, including best practices and FAQs. ...
 J. David Giese &
J. David Giese &
FeaturedArticleCybersecurity
Practical suggestions and tips for authoring SBOMs for medical devices and for using them to monitor for cybersecurity vulnerab...
 J. David Giese
J. David Giese
ArticleAI/ML
From solo clinicians prototyping algorithms to enterprise teams shipping production software, tools like Cursor, Claude Code, C...
 Yujan Shrestha
Yujan Shrestha
ArticleCybersecurity
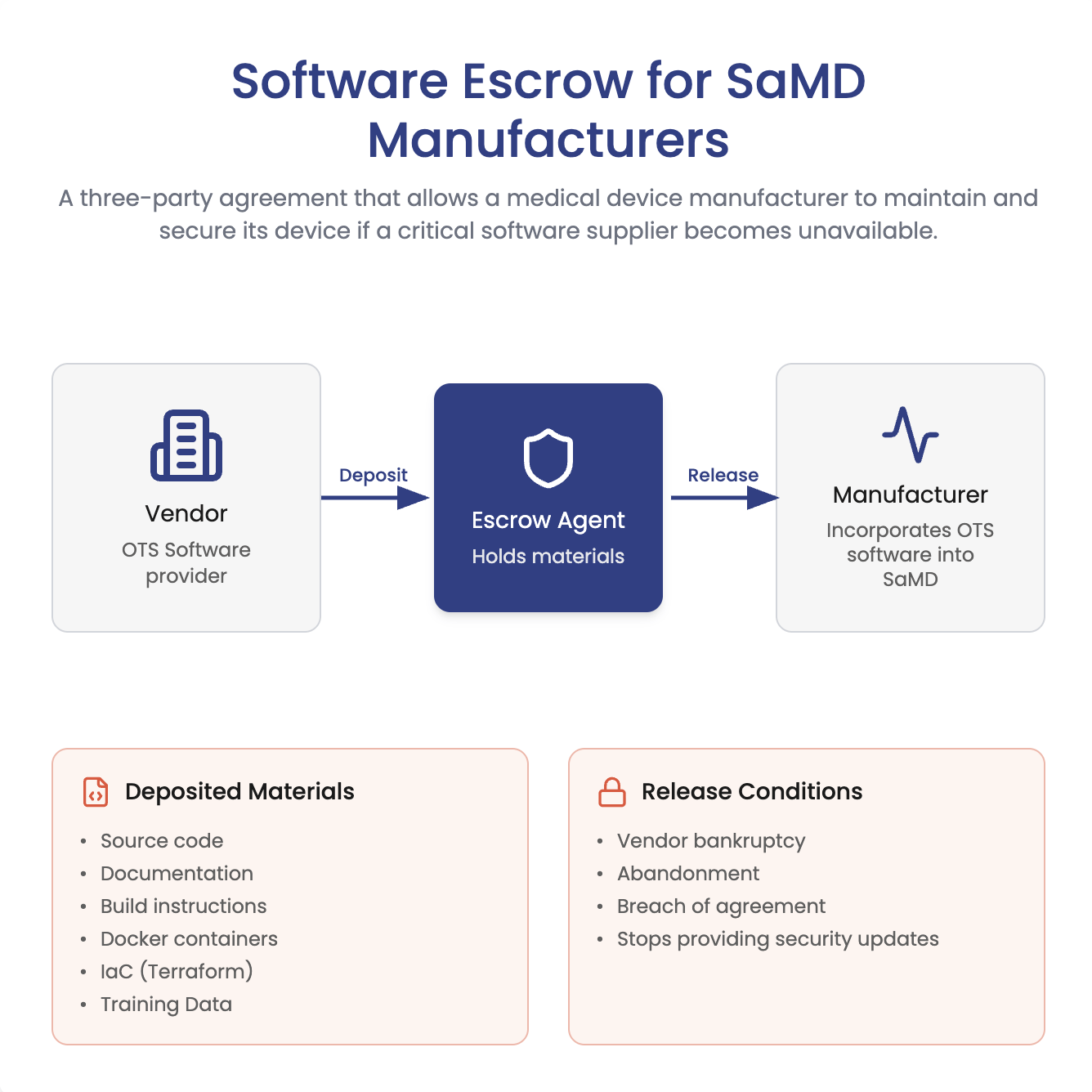
Does FDA require software escrow for SaMD? Not necessarily. Learn when escrow helps manage closed-source vendor risk, plus what...
 J. David Giese
J. David Giese
GuidanceCybersecurity
The 2026 FDA guidance on medical device cybersecurity, updated to align cybersecurity expectations with the Quality Management ...

ArticleAI/ML
A client called out the “consultant thing”: hiding behind “ideally” instead of recommending a real plan. This piece explains wh...
 Yujan Shrestha
Yujan Shrestha
ArticleAI/ML
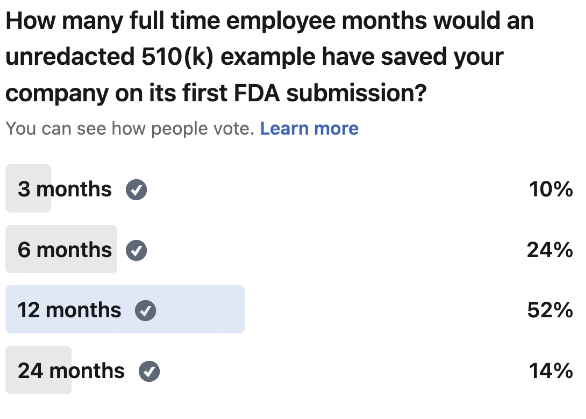
Most first-time teams burn over a year overbuilding documentation FDA never asks for. Here is a section-by-section breakdown of...
 Yujan Shrestha
Yujan Shrestha
ArticleCybersecurity
In this article, we share a nuanced approach to avoiding sharing sensitive information in an SBOM.
 J. David Giese
J. David Giese
VideoCybersecurity
The conversation between Yujan Shrestha and J. David Giese focuses on making threat modeling more approachable and less intimid...
 Yujan Shrestha & J. David Giese
Yujan Shrestha & J. David Giese
VideoCybersecurity
We discuss challenges in medical device cybersecurity, including balancing FDA guidelines with practical hospital and manufactu...
 Yujan Shrestha & J. David Giese
Yujan Shrestha & J. David Giese
ArticleCybersecurity
A survey that should give you a feeling as to whether you’re cybersecurity documentation is ready for an FDA marketing submission.
 J. David Giese
J. David Giese
ArticleCybersecurity
How do you avoid slowing down your FDA marketing submission (510(k), De Novo, or PMA) with cybersecurity problems? This article...
 Yujan Shrestha & George Hattub
Yujan Shrestha & George Hattub
ArticleCybersecurity
A technical exploration and discussion of DICOM Part 15 Security
ArticleCybersecurity
How safe is DICOM in the wild? As you develop your medical imaging device or service, prepare for the standards and regulations...

ArticleCybersecurity
A short article that attempts to explain why badly made diagrams will confuse FDA reviewers and slow down your submissions. Inc...
 J. David Giese
J. David Giese
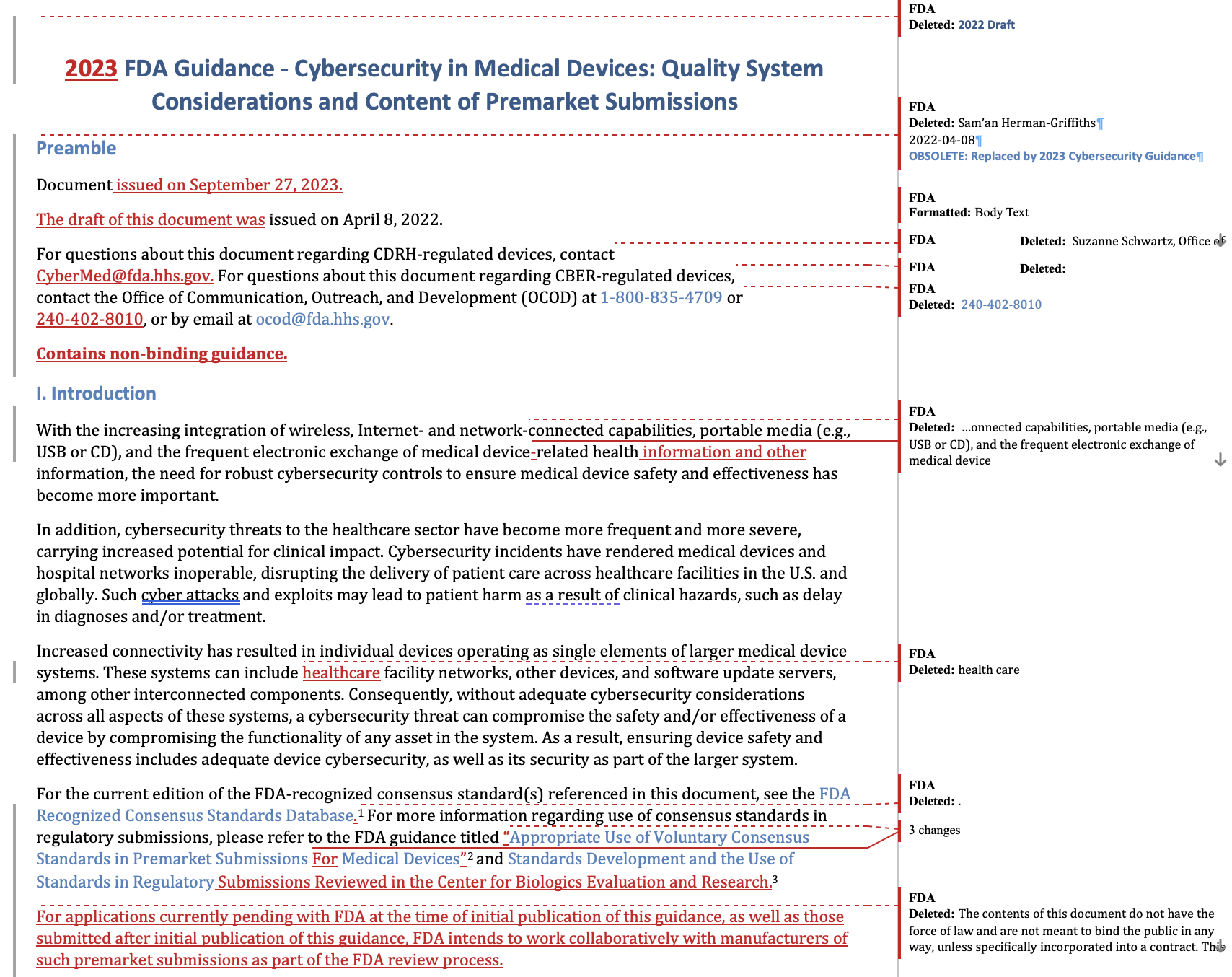
ArticleCybersecurity
This is a redline between the 2022 Draft cybersecurity guidance and the final 2023 cybersecurity guidance. It should be useful ...
 J. David Giese & Meri Martinez
J. David Giese & Meri Martinez
GuidanceCybersecurity
The long-awaited FDA guidance on cybersecurity, touching both on regulatory submissions and quality system considerations.
VideoCybersecurity
Security vulnerabilities in medical devices can have devestating consequences. They can lead to patient injuries and in the wor...
GuidanceCybersecurity
The FDA guidance discussing risks and documentation for pre-market submissions when devices must inter-operate with other devic...
GuidanceCybersecurity
This FDA guidance outlines recommendations for managing cybersecurity vulnerabilities in medical devices, including a risk-base...
GuidanceCybersecurity
This FDA guidance outlines how manufacturers should maintain the cybersecurity of medical devices that use off-the-shelf softwa...
There are no resources matching these filter criteria.

Get To Market Faster
Our Medtech tips will help you get safe and effective Medtech software on the market faster. We cover regulatory process, AI/ML, software, cybersecurity, interoperability and more.