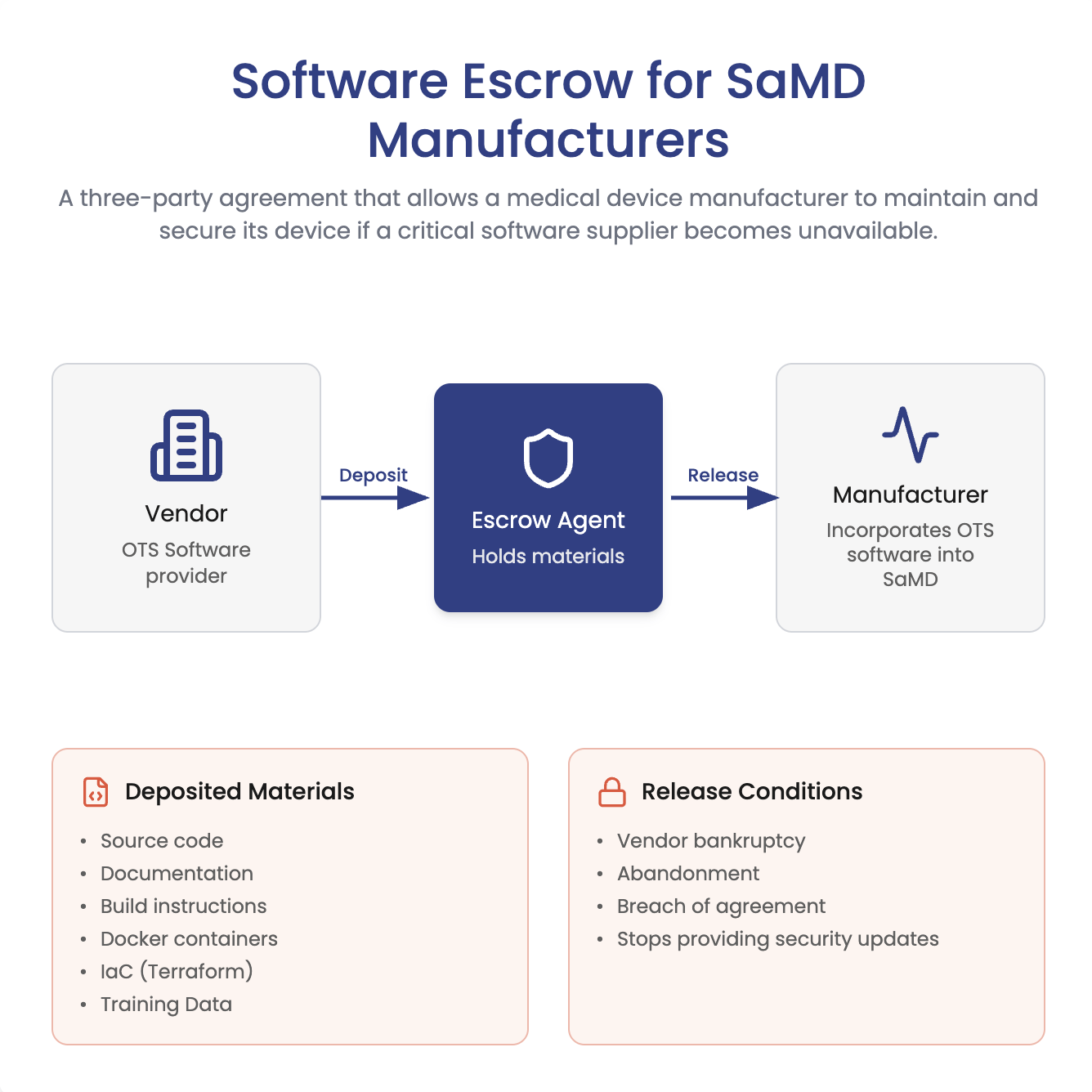
For many of us, escrow is associated with bad memories from paying a deposit on your house. In the finance, escrow means a third party holds funds until a transaction is complete, then releases them to the seller. Software escrow is similar. It involves having your vendor give key materials (often source code) to third-party. This third party holds them until a defined “release event” occurs.
Does FDA require SaMD manufacturers to use software escrow for their key vendors?
No, not necessarily. FDA cybersecurity expectations focus on managing third-party risk and maintaining the ability to remediate vulnerabilities over the product lifecycle. Software escrow is not a universal requirement, but it can be a valuable risk control when you rely on closed-source, difficult-to-replace third-party components. However, software escrow can be an important security risk control if you have critical vendors who provide close source software. (See this section of the FDA Cybersecurity Guidance if you’re curious about the guidance.)
Consider the following sequence of events:
- Your SaMD uses a closed-source third-party component that’s difficult to replace
- The vendor goes out of business, is acquired, or discontinues the product
- A vulnerability is discovered in the dependency
- You can’t patch quickly (or can’t replace the component fast enough)
- Threat actor exploits the vulnerability in your device!
Putting the source code in escrow at a third-party can mitigate this security risk. If the vendor stops supporting the product, the escrow agent can release the escrowed materials so your team (or a third party you hire) can maintain, patch, or rebuild the component as needed to protect patients and users.
As the diagram above implies, for SaMD it is usually not enough to escrow only source code. To ensure escrow mitigates the risk, you want the vendor to deposit everything required to build, verify, and maintain the software, such as:
- Build instructions and system documentation
- Dependency manifests and version pins
- Docker images or build containers
- Infrastructure-as-code (for example, Terraform HCL files) and deployment scripts
- Test suites, test data, and expected outputs
- For AI/ML components: training data (or a legally workable substitute), model artifacts, and training pipelines
- Security documentation and SBOMs, where applicable
- Quality records that matter for maintenance (for example, change history, known issues, and verification evidence)
How can you know, without seeing all this material, that you’ll have everything you need to build and maintain the software? This is a key problem with software escrow. You don’t want the vendor to go out of business and then to be stuck in the same place. To solve this problem, some escrow agents actually will provide verification services where they confirm you have everything you need to build the software.
What are some good companies, and how much does software escrow cost? 🔗
Software escrow is a niche service, so our first-hand experience is limited. However, based on our research, these providers may be worth a look:
Pricing varies widely based on what is being escrowed (source-only vs. full build environment), how frequently deposits are updated, and whether you add verification services. Many providers charge an initial setup fee plus an annual maintenance fee, with verification and frequent updates increasing cost.

